Appsian Helps Duo MFA Customers Align PeopleSoft to Zero Trust
Securing data is as crucial as controlling the access to enterprise applications. Leveraging the Appsian Security Platform, organizations can implement a Zero Trust policy that ensures data access is granted to users on a contextual basis. This could include a variety of factors such as – access location, device used, time of request, IP address. Coupled with Appsian’s granular, real-time logging and analytics solution, organizations can log what data is being accessed and capture the contextual parameters of access thereby accelerating incident response and remediation.
With Appsian + Duo rapid integration model, organizations can achieve Zero Trust without delay. In fact, many of our mutual customers implemented Appsian + Duo in less than 30 days with some going from initial installation and testing to go-live in 1 week.
Overview
Adding Multi-Factor Authentication to PeopleSoft is the next step in hardening the user authentication model – but for PeopleSoft applications, this typically requires a custom integration. Appsian Security Platform (ASP) allows customers to integrate Duo MFA with PeopleSoft via code-free configuration, and further extends the value of MFA with context-aware enforcement policies.
Capabilities
First Steps
- 1. Sign up for a Duo account
- 2. Log in to the Duo Admin Panel and Navigate to Applications
- 3. Click Protect an Application and locate Appsian ASP in the applications list. Click Protect this Application to get your integration key, secret key, and API hostname. (See Getting Started for help.)
Note: If integrating multiple applications (such as PeopleSoft Campus Solutions or PeopleSoft Human Capital Management) with Duo, each application can be integrated using a single Appsian ASP application – or, each application can be configured uniquely as a separate Appsian ASP application.
Protecting an Application
https://duo.com/docs/protecting-applicationsConfigure Duo in Appsian Security Platform for PeopleSoft
To create Rules resulting in the display of Duo challenges, ASP is first configured to use the API and keys unique to a customer Duo implementation. This configuration is done via the related Provider Profile pages using the following navigation:
Appsian > Application Security Platform > Telephony / Integrations > Duo
After creating a new value to represent the application, the following Provider Profile configuration page is displayed:
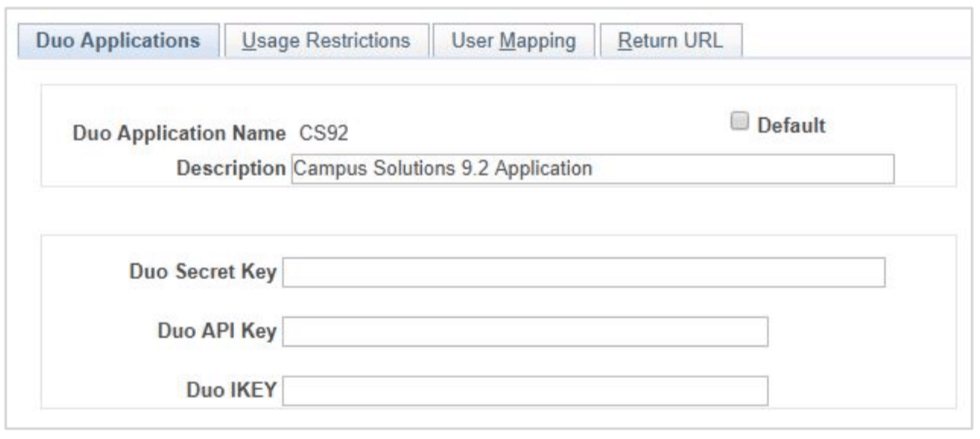
Duo Keys
All of the key values supplied on the Duo Applications tab come directly from the Duo Admin Panel as part of the customer Appsian ASP application.
The Duo API Key represents a web service endpoint shared by all customer applications, so if integrating Duo challenges with the ASP in many applications, this value is consistently configured for each application. However, both the Duo Secret Key and Duo IKEY are tied to unique Appsian ASP applications.
Recommendation: As described in the Duo documentation, the Duo Secret Key should be treated like a password. Do not share or email this data. If compromised, the value can be reset via the Duo Admin Panel and then reentered on this configuration page.
Tip: To further protect a production Duo Secret Key, it can be helpful to use one key for a production environment and a shared key for non-production environments. This separation will also segregate production usage statistics from non-production statistics.
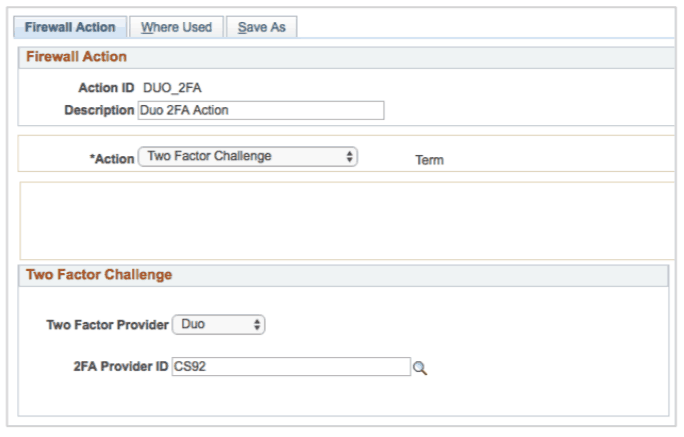
Creating a Rule with the Duo 2FA Action
Like other use cases modeled with the ASP, a Rule is created to define the Conditions whereby the Duo challenge is presented. This Rule is created with the action type of 2FA Action.
In the screenshot below, the 2FA Action DUO_2FA is connected to the CS92 2FA Provider ID.
Additional Resource
Enable Zero Trust in Oracle PeopleSoft
Organizations are moving to a zero trust authentication model to manage the business risks created by the myriad of users (and devices) accessing sensitive business data. For traditional, on-premise ERP applications like Oracle PeopleSoft, establishing a deep integration that enables zero trust through multi-factor authentication (MFA) presents significant challenges View
Troubleshooting
Need some help? Try searching our Knowledge Base articles or Community discussions. For further assistance, contact Support.






